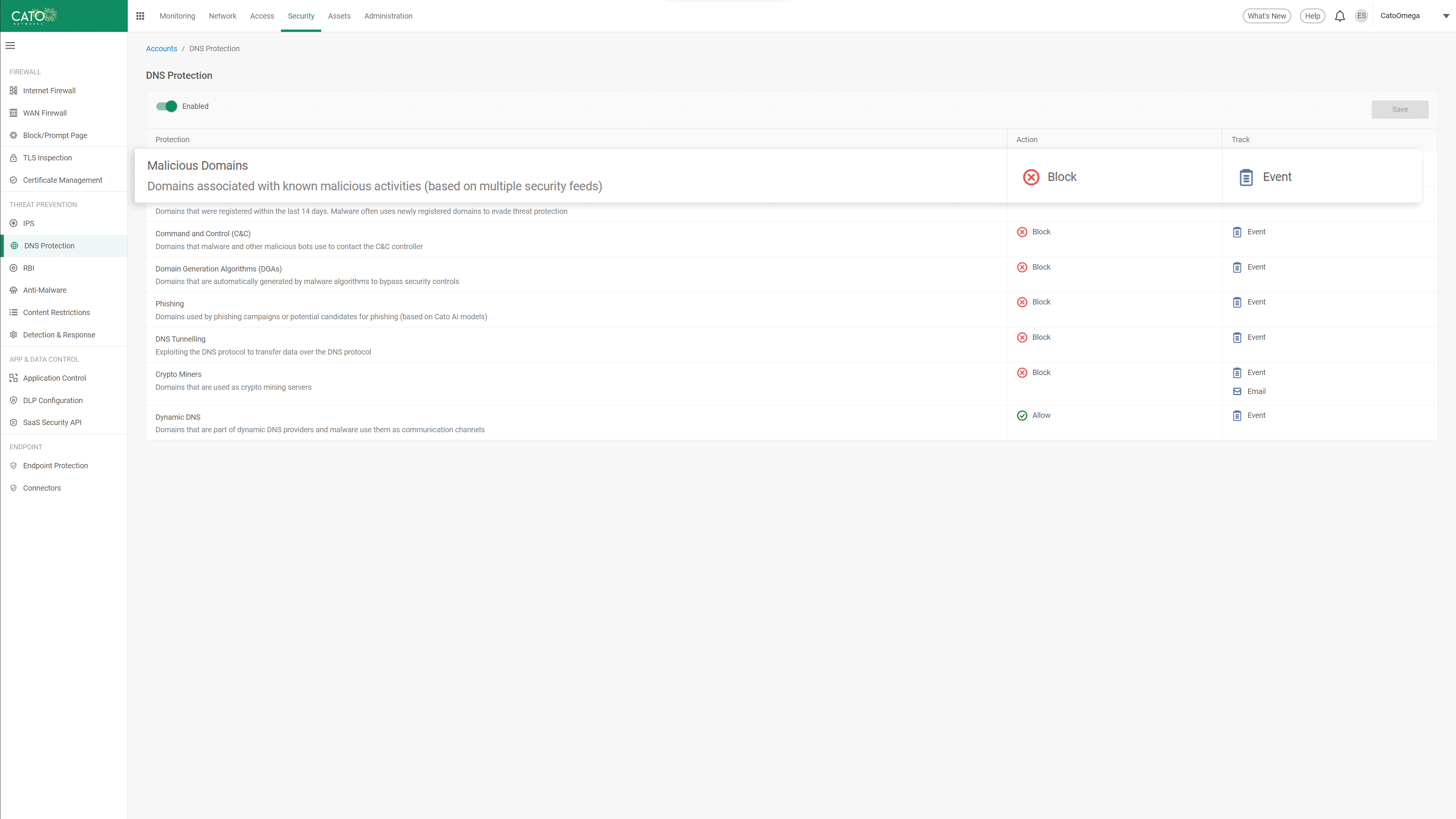
DNS Security
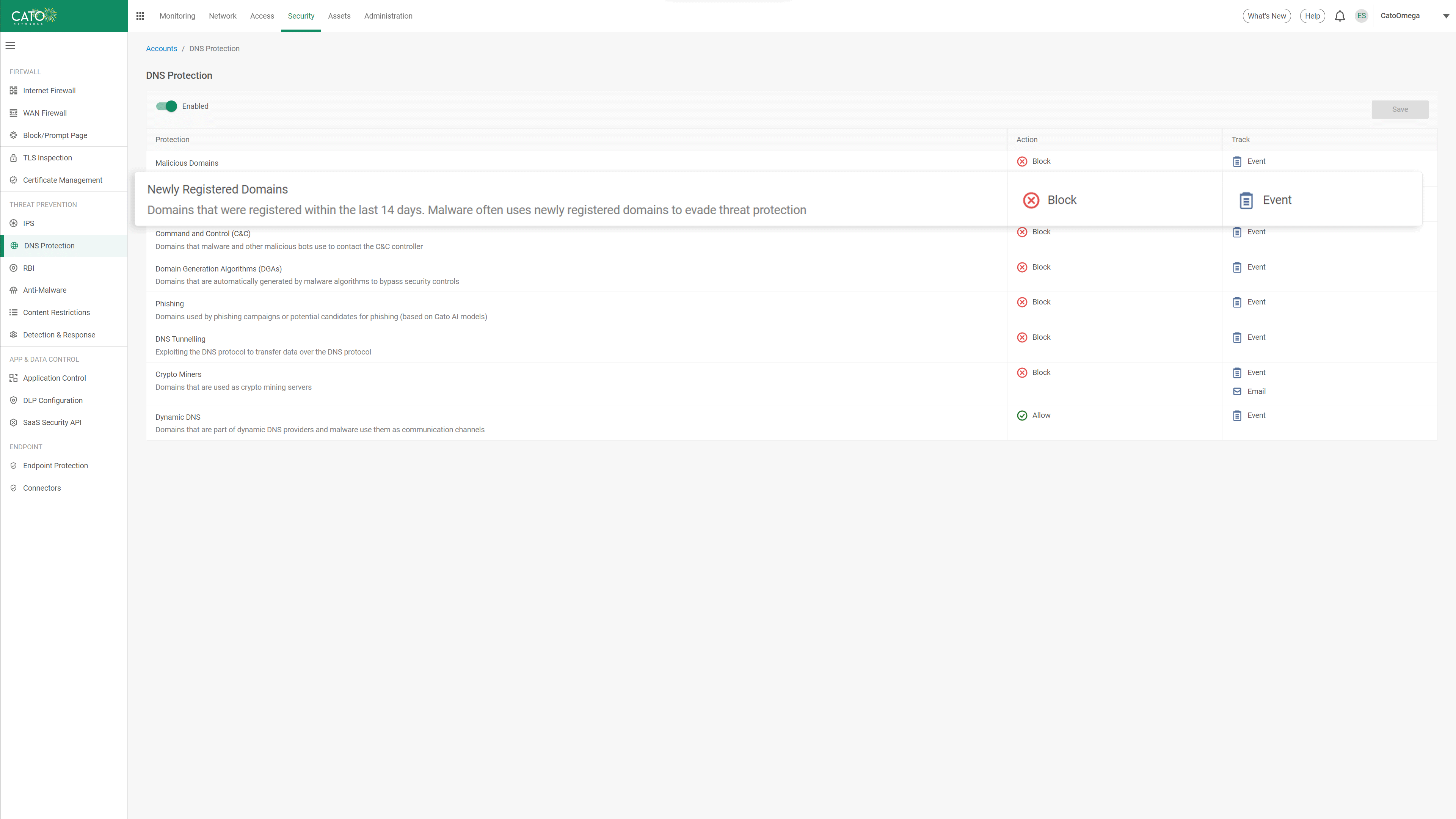
Cato’s DNS Security inspects all DNS traffic, preventing malicious DNS activity hiding within the protocol’s traffic, and blocking DNS requests to malicious destinations before a connection is made.
DNS Security Capabilities
AI-based DNS Inspection Deliver Superior In-line Phishing Protection
Phishing is one of the top attack vectors that every CISO is concerned about.
Ongoing training of AI and ML algorithms on Cato’s massive global data lake enables Cato DNS Security to provide in-line identification of domain squatting and other website impersonation attempts. This is achieved through real-time analysis of webpage components, domain age, popularity, and patterns associated with toolkits used in phishing sites. This Inline detection of phishing attacks helps prevent credential harvesting, malware delivery, and sensitive data loss.
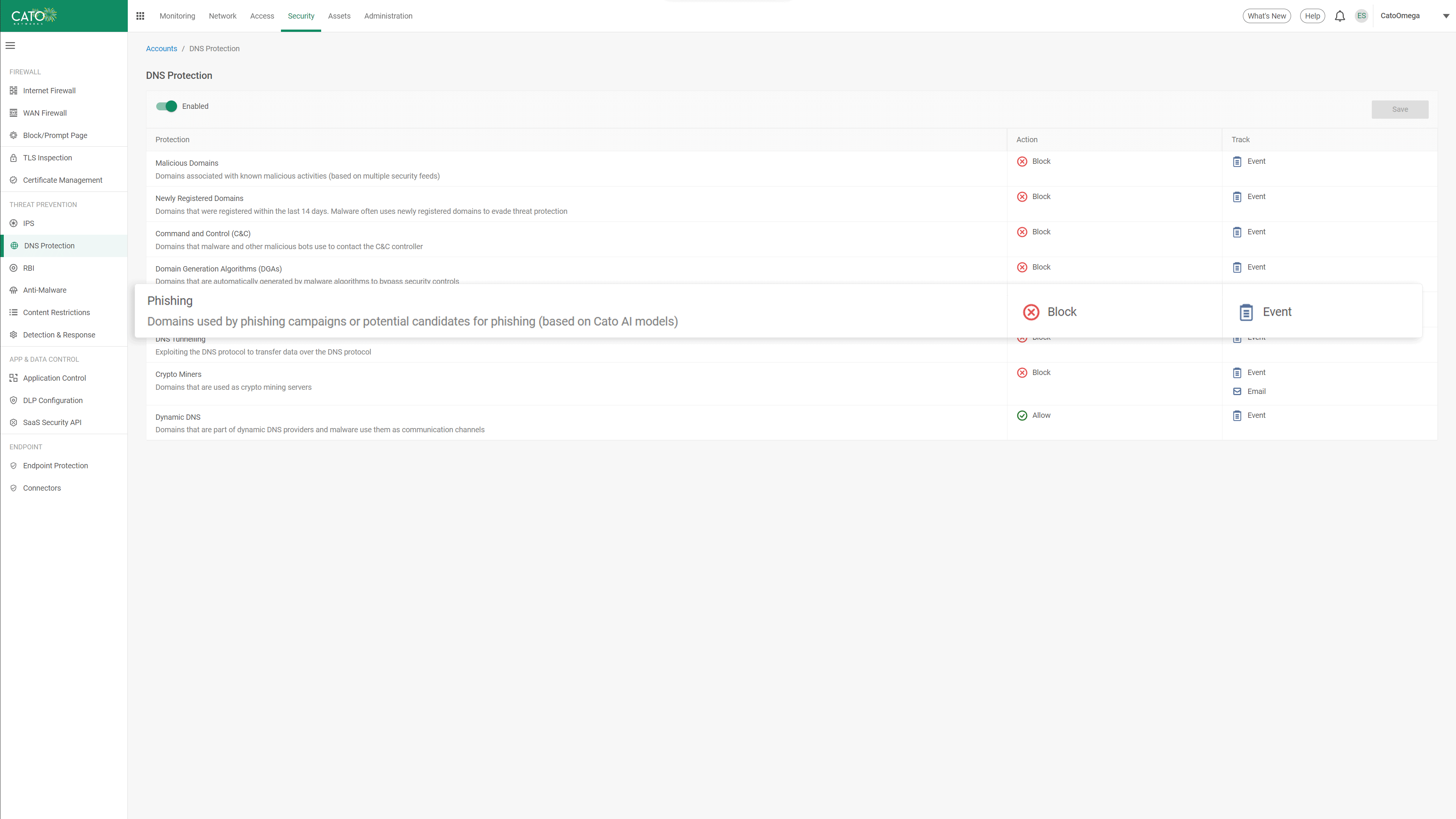
Block Malicious Domains and C&C Sites Before Connection
The number of malicious sites that host command and control (C&C) servers to remotely manage malware is huge. Attackers continuously move their C&C servers between sites to avoid detection and blacklisting. Cato DNS Security uses Cato’s timely and continuously optimized threat intelligence system to identify malicious domains and C&C sites and block traffic to and from them in real time. Using Cato DNS Security, enterprises dramatically reduce exposure to millions of web-based attacks with near-zero false positives.
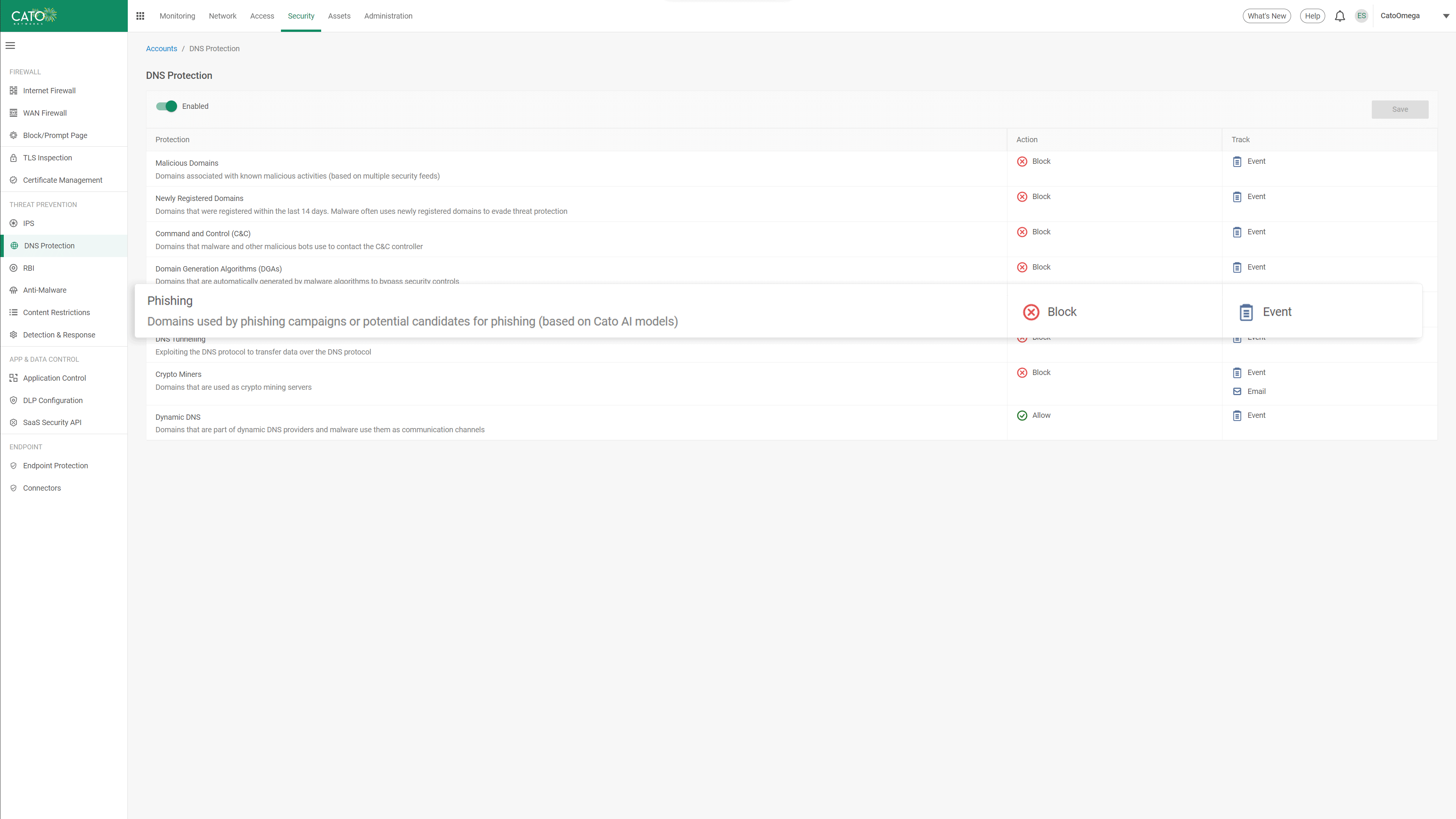
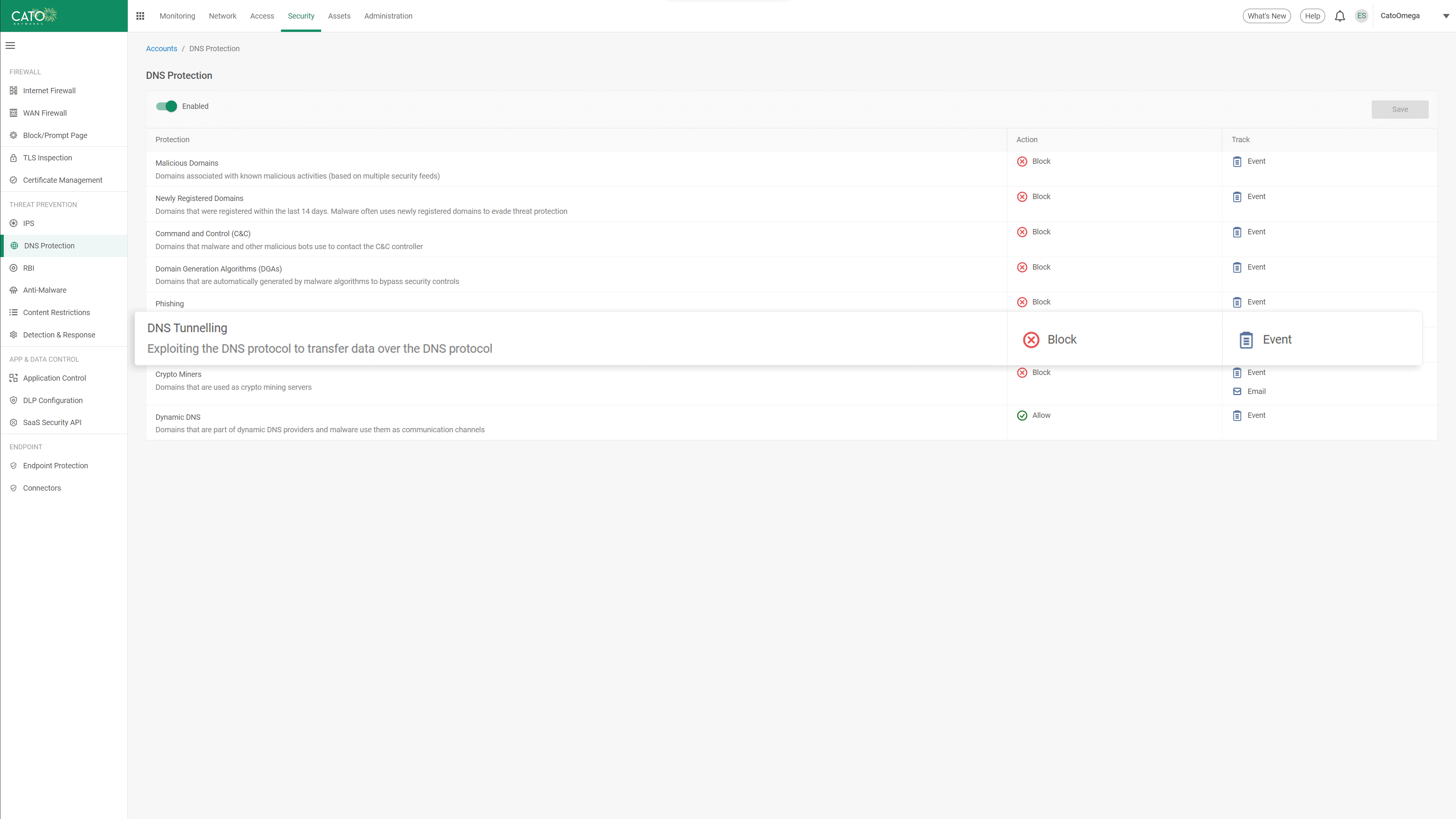
Stop Data Loss and Malicious Activity over DNS Tunneling
DNS tunneling attacks leverages the need to allow DNS traffic to pass through security controls, as a method for data exfiltration and C&C access. Cato’s DNS Security analyzes DNS request properties such as packet size, record type, and the ratio of unique subdomains to identify anomalies and indicators of DNS tunneling attacks. Cato’s AI/ML algorithms are continuously trained to identify DNS Tunneling, enabling protection that is not dependent on specific knowledge of the threat actor or domain name.
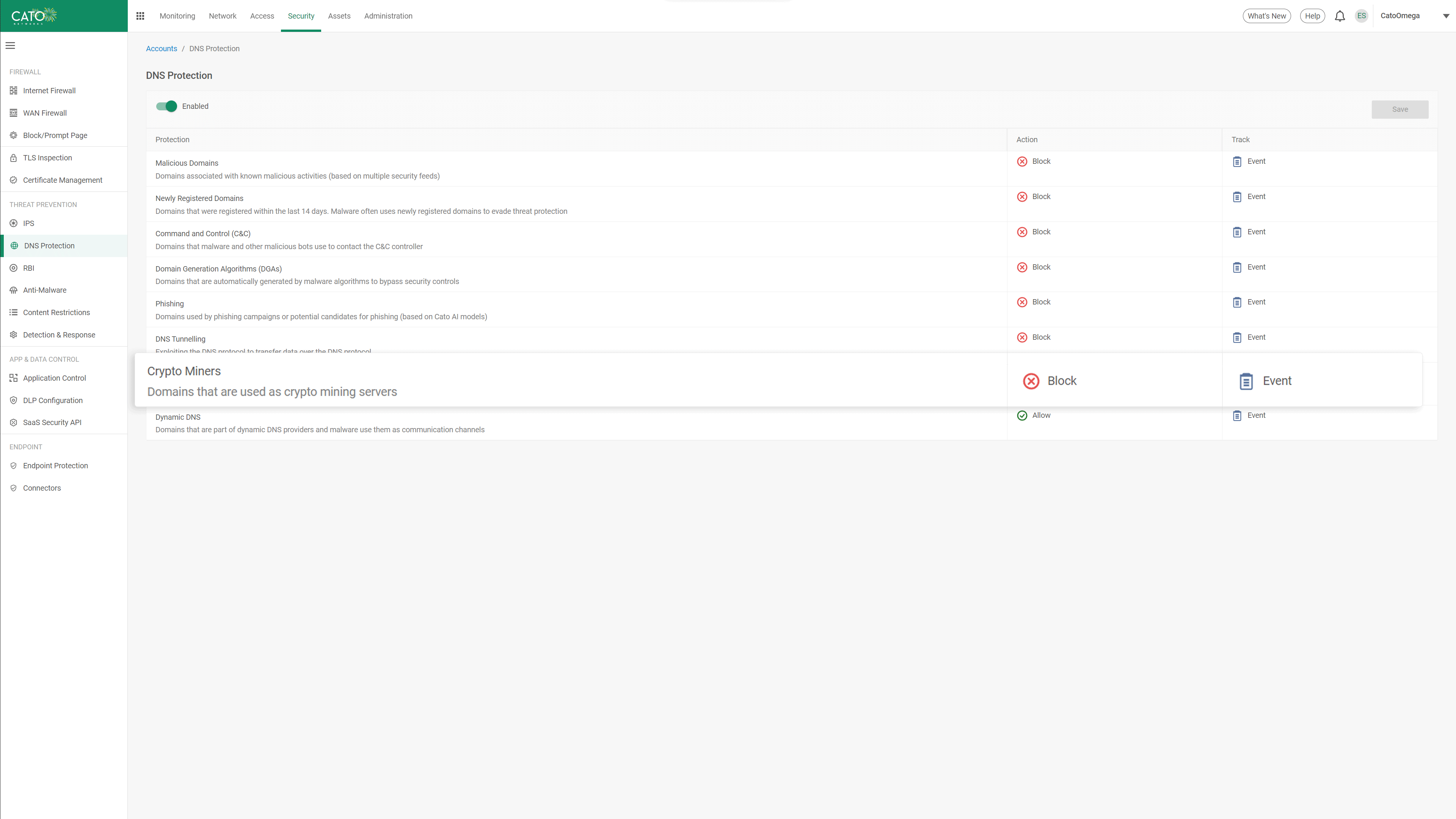
Prevent Resource Leaching from Crypto Miners
Crypto miners use compromised corporate endpoints for financial gain leading to system instability, poor user experience, and increased costs for the organization. Cato leverages dedicated rules and heuristics to identify domains that are used for crypto-mining operations, blocking any DNS requests to these destinations. With Cato, enterprises protect users’ productivity and security from impact by unauthorized use.
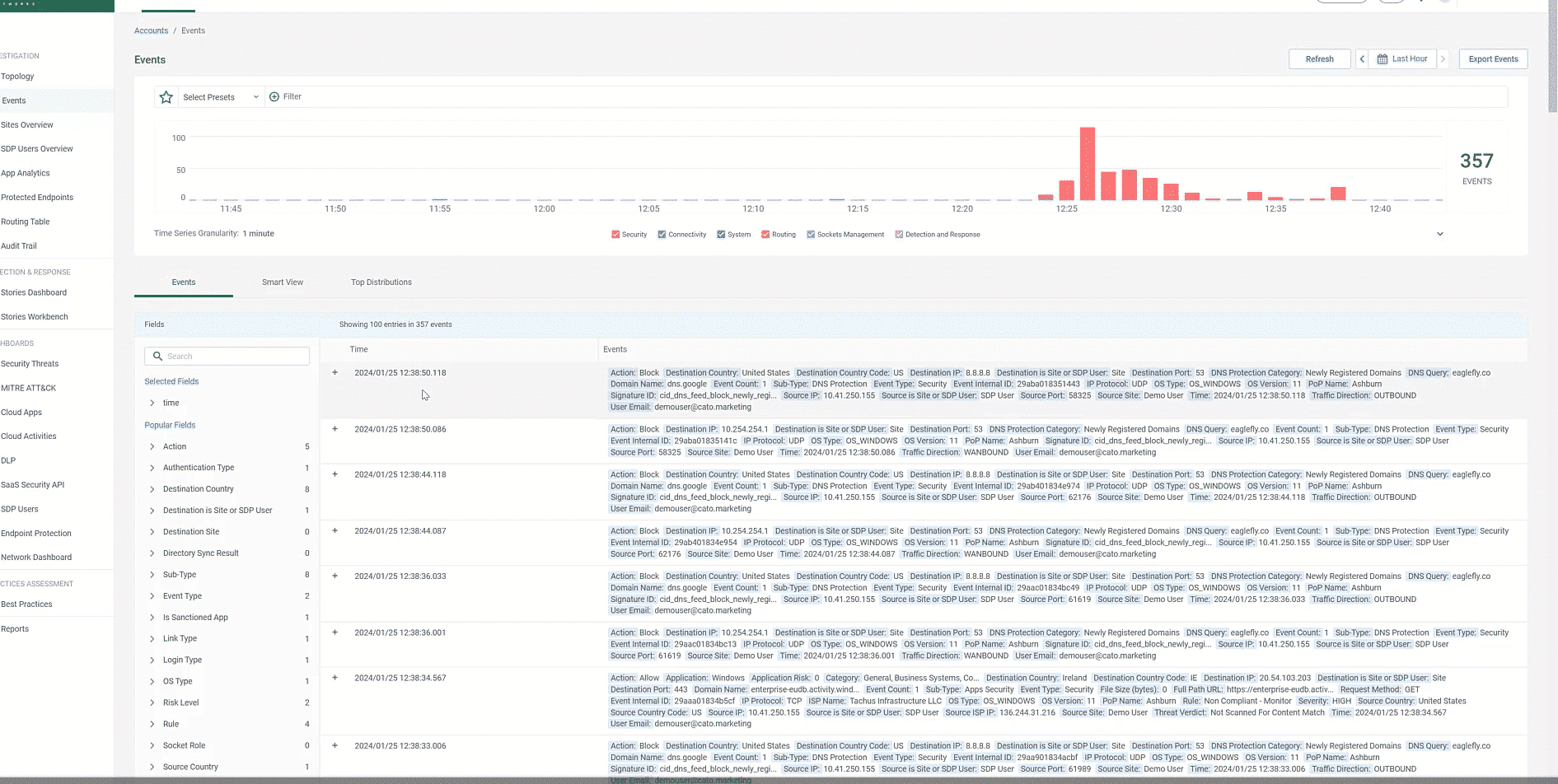
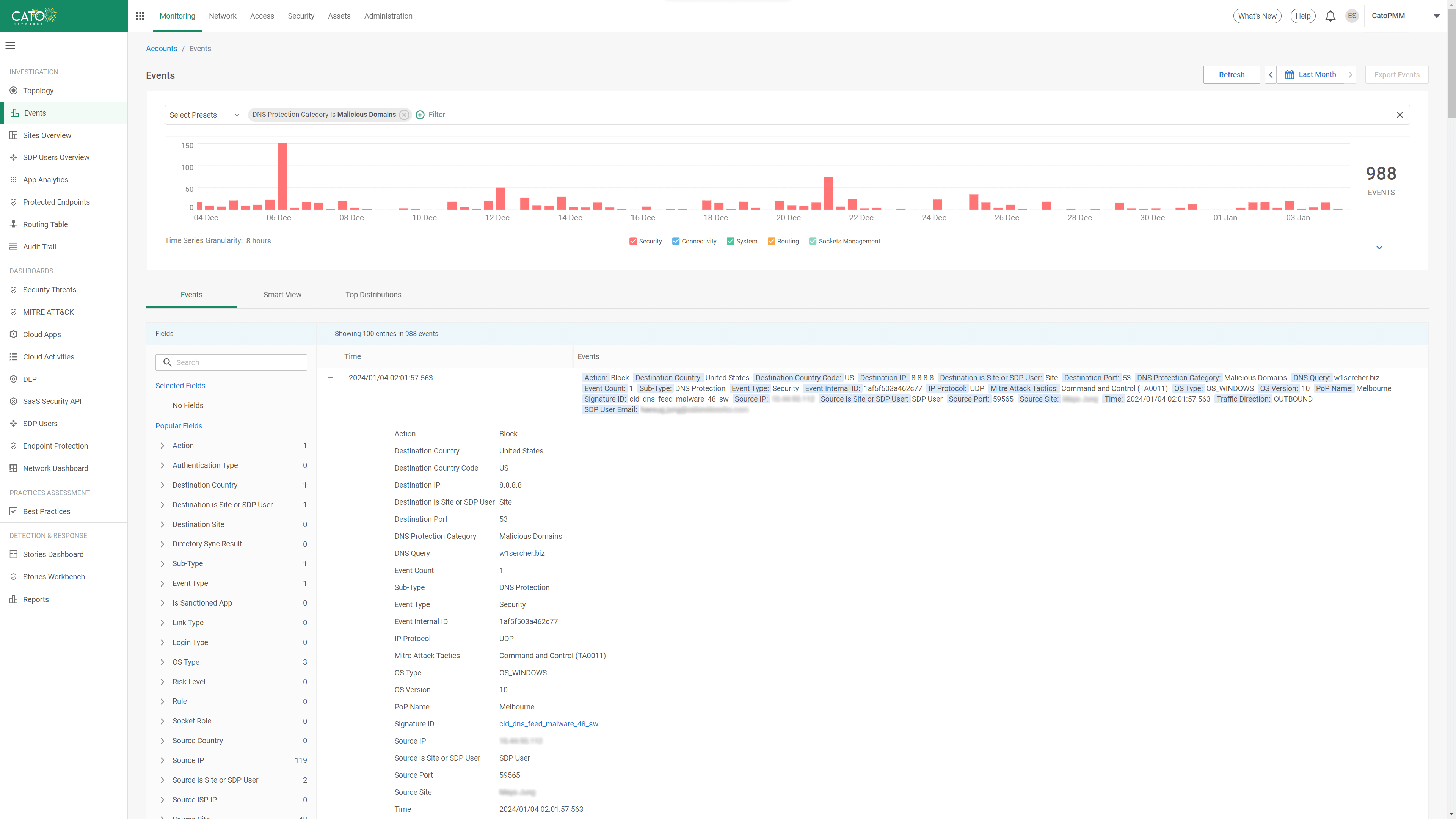
Full Visibility into DNS Security Threats and Events
All threat activity is logged in Cato’s global data lake, providing administrators with instant access to the threat information they need via a single console. DNS security events are visible in the security threats dashboard with filtering and drill down capability into all events related to DNS protection. Security teams can quickly understand and evaluate DNS threats to their organization without aggregating multiple data sources or navigating between multiple consoles.
La plataforma en la nube SASE de Cato empodera a los negocios digitales
Los clientes usan Cato para eliminar las complejas arquitecturas clásicas, compuestas de varias soluciones puntuales y de costosos servicios de redes.
La plataforma SASE de Cato es única y ofrece de forma autónoma y constante un acceso a aplicaciones optimizado y seguro en todas partes y para todo el mundo.
Cato Networks ha sido nombrada líder en Magic Quadrant™ de Gartner® 2024 para SASE de un solo proveedor
«Cato Networks es el punto de referencia para ZTE y SASE»
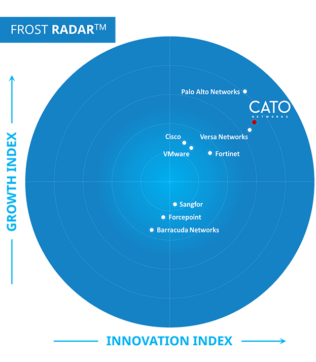
Cato Networks ha recibido el reconocimiento de ser líder en crecimiento e innovación de SASE
El SASE de Cato ha sido identificado como líder en el informe Radar de GigaOm
Cato Networks ha sido reconocida como líder de producto SSE global
La transformación WAN con SD-WAN: Establecer unos cimientos sólidos para el éxito de SASE


«Ejecutamos un simulador de filtraciones y ataques. Los índices de infección y los movimientos laterales cayeron en picado a la vez que los índices de detección subieron. Esos fueron factores clave por los que confiamos en la seguridad de Cato».
Prueba Cato
La solución que los equipos de TI han estado esperando.
¡Prepárate para que te sorprendan!