- SASE
- Platform
- Platform Architecture
- Core Components
Converged single pass processing, purpose built global cloud service, and open data platform.
- Design Principles
360-degree visibility and control, autonomous life cycle and posture management, gradual low risk deployment, and universal management.
- AI-powered SASE
Built-in (not bolted-on) AI is used across every aspect of the platform, from operational tasks to advanced security
- Core Components
- Platform Capabilities
- Platform Features
- Platform Architecture
- AI & Security
- Use Cases
- Customers
- Partners
- Managed Services
- Company
- Resources
- SASE
- Platform
- Platform Architecture
- Core Components
Converged single pass processing, purpose built global cloud service, and open data platform.
- Design Principles
360-degree visibility and control, autonomous life cycle and posture management, gradual low risk deployment, and universal management.
- AI-powered SASE
Built-in (not bolted-on) AI is used across every aspect of the platform, from operational tasks to advanced security
- Core Components
- Platform Capabilities
- Platform Features
- Platform Architecture
- AI & Security
- Use Cases
- Customers
- Partners
- Managed Services
- Company
- Resources
Cato SASE Cloud Platform Capabilities
Cato SASE optimally and securely connects all enterprise locations, users, applications, and clouds, into a global and secure, cloud-native platform. Cato can be gradually deployed to replace security point solutions and legacy network services.
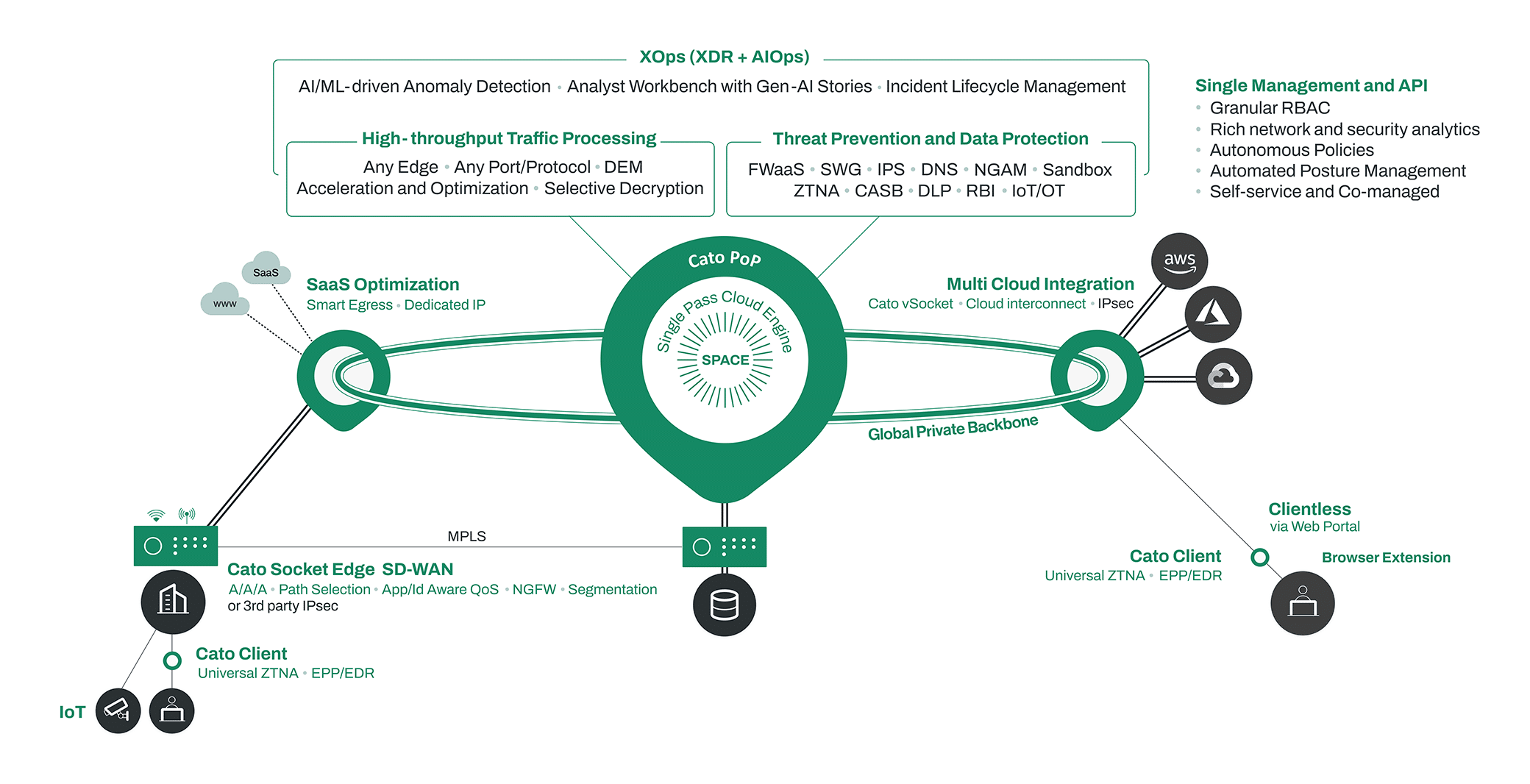
Connect Everything
Cato SASE consolidates all enterprise traffic, WAN, internet, and cloud, into a consistent, optimized, and resilient cloud network. Cato offers a range of cloud on-ramps to easily connect physical locations, end users, and cloud datacenters to the cloud network.
Consistent and Optimized Cloud Network
Global Private Backbone
Cato’s SLA-backed global private backbone underpins the global Cloud Network. The backbone is comprised of a dense footprint of physical Points of Presence (PoPs) hosted in regional top-tier datacenters and interconnected with multiple global and regional carriers. The backbone is designed to provide massive, fully encrypted, SLA-backed global connectivity through a consistent and predictable underlying network transports. Cato’s deep network engineering and operations expertise enables the optimal selection and integration of hosting providers and carriers into the backbone.
Global Traffic Optimization
Cato applies optimization and acceleration to all traffic going through the backbone to enhance application performance and the user experience. To ensure all users and locations benefit from the backbone capabilities, Cato optimizes traffic from all edges and towards all destinations (on premises and in the cloud). With this design Cato supports latency sensitive traffic such as voice, video, and transactional and legacy applications, to enable optimal user productivity. For SaaS traffic, Cato provides granular control of application traffic routing to ensure traffic is delivered via the optimized backbone to the PoP nearest to the application instance.
Digital Experience Monitoring
Cato DEM empowers IT teams to support the digital business while minimizing user experience issues. Using real-time monitoring, IT teams can troubleshoot user experience issues with end-to-end visibility and improve efficiency. Synthetic probing combined with AI/ML enables proactive monitoring and mitigation of experience issues before they are reported by users. Cato DEM covers all the applications used by the enterprise across internet, SaaS and WAN. No sensor deployment, installation or integrations are required.
Cloud On-Ramps
Cato Socket SD-WAN Device for Physical Locations
A full-fledged SD-WAN solution, the Cato Socket delivers access resiliency across multiple links, application aware quality of service, and automated high availability for local and cloud connectivity and failover scenarios. The Cato Socket connects a physical location to the nearest Cato PoP via one or more last mile connections. Customers can choose any mix of fiber, cable, xDSL, and cellular connections. The Cato Socket applies multiple traffic management capabilities such as active-active link aggregation, application- and user-aware QoS prioritization, dynamic path selection to work around link blackouts and brownouts, and packet duplication to overcome packet loss. The Cato Socket can also route site-to-site traffic over MPLS and the Internet to address gradual migration, regional and application-specific requirements.
Cato Client and Clientless Access
Cato provides an endpoint client for Windows, Mac, iOS, Android, and Linux. It enables secure and optimized remote access to private applications under the continuous inspection and control of the Cato SSE 360 security stack. The Cato Client can further secure the endpoint through an EPP/EDR engine that is seamlessly managed by the Cato Management Application. Lastly, clientless access is available through a secure web portal for users, such as external contractors, that can’t deploy the client.
Cross Connect, Virtual SD-WAN Device, Cloud IPSec
Cato provides multiple options to connect cloud datacenters to the Cato SASE Cloud Platform. These include a Cato vSocket virtual SD-WAN device that can be deployed in the cloud datacenter, a direct cross-connect from the cloud provider to the Cato PoP, and the creation of an IPSec tunnel between the Cato PoP and the cloud provider’s datacenter VPN edge.
Any IPSec-enabled Device
Existing IPSec enabled devices, such as routers and edge firewalls, can be used to forward traffic from physical locations to the nearest Cato PoP. While Cato’s SD-WAN capabilities do not apply, customers will benefit from Cato’s cloud-first architecture and the traffic will be fully secure and optimized by the Cato SASE Cloud Platform including the optimized cloud network and cloud-delivered security services.
Protect Everywhere
Cato embedded a full security stack, SSE 360, into the cloud platform to address the distribution, scaling, resiliency, and enforcement of unified security policies everywhere and on everyone. Cato further extends protection to the endpoint for end-to-end threat prevention and detection.
Network Security
SSE 360 – Security as a Service
Cato SASE Cloud Platform includes a cloud-native security stack, SSE 360. It is based on Cato’s Single Pass Cloud Engine (SPACE) architecture and converges the following capabilities: network segmentation and zero-trust (FWaaS), threat prevention (SWG, IPS, Malware Prevention, DNS Security, RBI), and application and data protection (CASB, DLP, ZTNA). Cato’s SSE 360 is built to decrypt and inspect all enterprise traffic, without the need for sizing, patching, or upgrading of appliances and other point solutions. Security policies and events analysis are centrally and uniformly managed using the self-service Cato Management Application.
Network Segmentation and Zero Trust
The most fundamental security capability of Cato’s SSE 360 is Firewall as a Service (FWaaS). FWaaS controls traffic flow, across all ports and protocols, and in all directions both WAN (east-west), and the Internet (south-north). Firewall policies are used to segment the network based on network resources (such as VLANs) and logical elements such as identity, organizational units, applications, and services. Network segmentation in conjunction with continuous traffic inspection enables customers to sustain a zero-trust security posture.
Multi-Layer Threat Prevention
Cato implements defense in depth with multi-layer threat prevention capabilities. Secure Web Gateway (SWG) protects users against risky web sites, phishing attacks and malware delivery. Intrusion Prevention System (IPS) detects and stops malicious traffic based on threat intelligence feeds, AI/ML inline controls, and deep heuristics that leverage granular context including identify, network, application, and data attributes. Malware Prevention engine inspects every payload to stop inbound infections. DNS security inspects DNS queries and responses to prevent DNS tunneling and to block phishing attacks, malicious domains, malware communication and other DNS-based threat vectors. Remote Browser Isolation (RBI) further protects users by directing traffic to high-risk web sites into an isolated cloud-based browser session, thus minimizing the risk of endpoint compromise.
IoT/OT Security
Cato IoT/OT Security extends comprehensive protection to IoT and OT environments, providing real-time device discovery and classification, granular policy enforcement, and holistic threat prevention. As a native feature of the Cato SASE Cloud Platform, Cato IoT/OT Security eliminates complex integration and simplifies management.

Application and Data Protection
Cato enforces application access control and data protection on all access, both inline and out-of-band through SaaS API integrations. Cato Cloud Access Security Broker (CASB) provides broad visibility to the usage of both sanctioned and unsanctioned (“Shadow IT”) applications and the ability to enforce access policies based on application, user, and device risk. Data Loss Prevention (DLP) engine enforces access policies and granular actions on sensitive data across on-premises and cloud destinations from corporate and BYOD devices.
AI Security
Secure Use of Public AI
Cato enables enterprises to securely harness the power of Public GenAI applications without compromising security or compliance. With comprehensive visibility into every AI interaction, Cato discovers and categorizes all GenAI usage across web, API, and applications, mitigating Shadow AI risks. By enforcing granular, intent-based usage policies and real-time detection of sensitive data violations, enterprises can confidently embrace third-party AI services. Cato’s AI usage controls ensure consistent governance, proactively preventing data leakage, limiting misuse, and reducing risk exposure, empowering safe adoption of innovative AI-driven use-cases.
Securing Private AI Models and Agents
Cato safeguards homegrown AI applications and agents against evolving threats. Leveraging purpose-built detection engines, Cato identifies runtime AI attacks, including prompt injections, jailbreaks, data leakage, and malicious interactions. Enterprises gain centralized, real-time visibility, enabling rapid response and reducing operational and reputational risks. Flexible deployment—via AI gateways or APIs—ensures seamless protection across cloud, on-premises, and edge environments. Cato protects internally developed AI, maintaining secure, compliant operations without hindering innovation or productivity.
Endpoint Security
Cato Client for Endpoints
Cato extends access control and endpoint protection, detection and response to user devices using the Cato Client. The Cato Client is available for all major operating systems and is delivered though IT software distribution or as a self-service deployment. The Cato Client provides granular endpoint traffic management capabilities to selectively control WAN and internet traffic using Cato. It also supports always-on mode to ensure corporate endpoints are continuously protected.
Hybrid and Remote Work
The Cato Client Universal Zero Trust Network Access (ZTNA) capability enforces the organization’s risk-based application access policy, in the office, on the road, and at home. Cato ZTNA provides extensive device posture analysis and integration with multiple identity providers to ensure full authentication and compliance with corporate policies before application access is granted and throughout the session. Once the user is connected, all traffic is continuously inspected by Cato SSE 360 for threat prevention and data protection.
Endpoint Protection, Detection, and Response
The Cato Client includes an Endpoint Protection, Detection, and Response (EPP/EDR) capabilities. Customers can extend protection to the endpoint itself using a next generation anti-malware engine that detects malicious files and correlates on-device suspicious activity. The Cato Client delivers endpoint risk context and events to a cloud-based data lake. Correlated with the detailed network context provided by Cato SSE 360 engines, Cato XDR creates an accurate picture of security incidents across endpoint and network domains.
Detect What’s Hidden
Cato leverages its granular network, security, and endpoint context and events to deliver a complete Threat Detection Investigation and Response (TDIR) life cycle management.
Incident Life Cycle Management
AI/ML-Driven Incident Detection
Cato leverages its granular data set of network, security and endpoint events, proven AI/ML capabilities for anomaly and threat detection, and incident analysis and response tools to deliver a full XDR solution. Cato consolidates incident data generated by the Cloud Network and the Cato Client, as well as 3rd party EPP/EDR solutions, such as Microsoft Defender for Endpoints, into a unified, cloud-based data lake. Cato’s threat hunting, user behavior analysis and network degradation detection algorithms analyze the data to identify and prioritize incidents for further review. Cato XDR generates unique insights and recommendations based on similar incidents detected across multiple customers to improve accuracy and incident prioritization.
AI-assisted Incident Investigation and Response
Cato integrates its incidents detection engine with Gen-AI to produce human readable “incident stories” that are made available through an analyst workbench. The workbench enables analysts to access granular details on the incident, consult AI-generated analysis based on insights from similar incidents, collaborate on incident resolution, and investigate related activity during the incident timeline. With Cato XDR, customer’s and partner’s analysts can leverage proven investigation and response capabilities already in use by Cato’s analysts delivering a managed extended detection and response (MXDR) service since 2019.
Managed Extended Detection and Response
For customers who prefer to partner with incident detection and response specialists, Cato and its partners offer a managed service that includes timely detection of threats, recommended remediation actions, and optional preventive measures. Cato’s MXDR ensures early detection of compromised endpoints to minimize threat dwell time, thus reducing the exposure to data breach and offloading a complex and time-consuming task from IT security.
Run Like a Champ
Management, Analysis, and Integration
Cato Management Application: Single Pane of Glass
The Cato SASE Cloud Platform is managed through the Cato Management Application, a single pane of glass to manage all policy configuration, network and security analytics, and real-time monitoring and troubleshooting. Cato scales its cloud-delivered management platform to store and process massive volumes of data and provide a high-performance interface to access and investigate all events data generated by the customer’s infrastructure. All current and future Cato capabilities are managed in the same way to ensure easy adoption by IT and quick delivery of new capabilities to the business.
Cato Universal API and 3rd Party Integration
The Cato API enables configuration and analysis automation, and data sharing and integration with 3rd party systems. Using the API, customers can extract selected events from the Cato data lake and feed them into external data stores for further reporting or analysis. The API also provides the ability to automate the creation of policies, users, sites, and other objects within the Cato platform to streamline provisioning of resources. Cato periodically releases formal integrations with different 3rd party systems for security analytics, enterprise workflow management, and ticketing systems.
The Strategic Benefits of a True SASE Platform
Architected from the ground up as a true cloud-native SASE platform, all Cato’s security capabilities, today and in the future, leverage the global distribution, massive scalability, advanced resiliency, autonomous life cycle management, and consistent management model of the Cato platform.
Consistent Policy Enforcement
Cato extends all security capabilities globally to deliver consistent policy enforcement everywhere and to everyone, from the largest datacenters down to a single user device.
Scalable and Resilient Protection
Cato scales to inspect multi-gig traffic streams with full TLS decryption and across all security capabilities, and can automatically recover from service component failures to ensure continuous security protection.
Autonomous Life Cycle Management
Cato ensures the SASE cloud platform maintains optimal security posture, 99.999% service availability, and low-latency security processing for all users and locations, without any customer involvement.
Single Pane of Glass
Cato provides a single pane of glass to consistently manage all security and networking capabilities including configuration, analytics, troubleshooting, and incident detection and response. Unified management model eases new capabilities adoption by IT and the business.
Cato SASE Cloud Platform Powers the Digital Business
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.


For me, Cato future proofs Swissport’s IT infrastructure. The platform constantly evolves, adapts to new technologies, and provides the visibility and security we need to support our business today and tomorrow.”
Richard Thorp
CTO
Swissport Elevates Security, Global Operations with Cato Networks


I would definitely recommend the Cato SASE platform to other companies. It makes our life really easy and helps us protect our business even further.”
Tal Arad
Chief Information Security Officer
Carlsberg Group Gains Flexibility and Visibility with Cato SASE

With Cato we have a good, solid sedan with the speed of a Porsche that got us exactly where we needed to go fast.”
Rodney Masney
Chief Information Officer
O-I Taps Augmented Reality and Cato SASE Cloud to Realize “Impossible-to-Count” Savings

With Cato, we got the functionality of SD-WAN, a global backbone, and security service for our sites and mobile users, integrated together and at a fraction of the cost”
Willem-Jan Herckenrath
Manager ICT
Alewijnse Transforms Global, Real-Time WAN with Cato Secure SD-WAN


Since we moved to Cato, our bandwidth increased by approximately 30 times the speed we had before. Now, the customer’s Wi-Fi experience is much better. We’ve stopped receiving complaints since deploying Cato”
Steve Waibel
Director of IT
Brake Masters Puts the Brakes on Outages Across 71 Sites with Cato


With Cato we have a very flexible supplier that understands our requirements and is there when we need help.”
Jan Jørgensen
IT Project Leader
Flügger Group Gains Network Flexibility and Security with Cato SASE Cloud

The big difference between Cato and other solutions is the integration of network management and security”
Yoshiaki Kushiyama
Senior Manager, Information Systems
Juki reduces network costs by using one security policy for all group companies

With Cato, we could move people out from our offices to their home offices fast without a single interruption”
Daniel Sollberger
Lead, Global Based IT Infrastructure
Komax Drives Innovation, Cloud Connectivity, and Mobile Collaboration with Cato


Cato allowed us the flexibility to incorporate our WAN, Internet and remote access solutions into one neat package that could be managed with a small team of people.”
Joel Jacobson
Global WAN Manager
Vitesco Technologies Builds New Global Enterprise Network with Cato


Cato’s management interface was so easy to use compared to those of the traditional SD-WAN players we looked at.”
Thomas Chejfec
Group CIO
Haulotte Reduced Costs and Improved Application Performance by Migrating from MPLS to Cato SASE


I see Cato SASE as a tool for digital transformation promotion. We can use it to reorganize our entire security portfolio, reduce costs, and bring out the best in our students, professors, and administrators. Being able to work productively and securely anywhere gives a great boost to all our digital transformation initiatives.”
Hitoshi Kusunoki
Information Planning Department
Waseda University Enables Universal Secure Remote Learning and Digital Transformation with Cato

Cato’s biggest benefit from my point of view is that our network operators no longer need any specialized knowledge.”
Takashi Nakajima
Head of the Digital Transformation (DX) Promotion Division and Chief of Business Operations
Topcon Achieves a Fast, Secure Global WAN with Cato


When we chose it over a year ago nobody was talking about SASE. Now, everybody is moving towards SASE and you can see it discussed in all the IT media.”
James Bonnaventure
CTO
Fidal Boosts WAN Performance, Cuts Costs in Half by Switching from MPLS to Cato

Now with Cato we just fire a support ticket and Cato is on it. Within 30 minutes to an hour it’s resolved. And we can monitor every single step with Cato’s QOS metrics. We have goggles and eyes we never had before.”
Kevin Juma
Technology Operations Manager
CloudFactory Boosts Network Scalability, Agility, and Security with Cato


With the Cato SASE Cloud from Cato Networks, we were able to connect locations and employees securely, easily and quickly. We now have the IT solution in-house and can adapt the infrastructure to our needs at any time with the desired flexibility.”
Ralf Luchsinger
Chief IT, Service and Provider Management
Cato SASE Cloud secures networking of Bank Avera locations and its mobile employees


Thanks to Cato, I can stand by my promises and feel comfortable we can deliver on the company’s business needs quickly, efficiently, and securely.”
Jesper Hjørland
Service Manager for Network and Connectivity
Fiskars Group Boosts Business Agility and Security with Cato SASE

I would recommend the Cato SASE solution to any healthcare organization that needs simple yet very secure connectivity among regional and local sites, remote users, and the cloud.”
Alvin Lim
Group Technology and Information Security Director
Fullerton Health Builds a Secure SASE Linking 550 Locations and the Cloud


I know that my company is secure, that all my sites and users can connect with the same solution, and that every time I need something from Cato, they’ll listen carefully and come through. Thanks to Cato I can sleep at night.”
Shira Baum
CIO
AFI Properties Cures Network, Security, and Remote Access Headaches with Cato SASE


We have improved the performance of every application on the network by rolling out Cato, We don’t hear about network slowness; we don’t hear complaints.”
Nick Hidalgo
VP, Information Technology
How Redner’s Markets Transformed the Retail Experience by Transforming its Network with Cato


There are not many times as a CIO that you can check the box in all these areas – faster, more secure, happy users, and a happy team – all for less cost and more business value. That’s the Cato SASE Cloud Platform.”
Dustin Collins
Global CIO
Chemical Manufacturer ESI Reduces the Time to Integrate Acquired Companies by 80% with Cato


The Cato team was interested in helping us succeed. After meeting their customer success manager and voicing our feedback on the product, Cato went out and changed the product. That’s what I call partnership.״
John Lim Ji Xiong
Chief Digital Officer
Gamuda Redefines IT Operations with the Cato SASE Cloud Platform


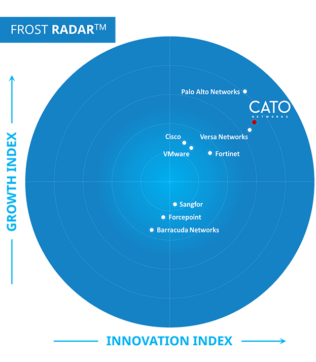
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.


“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
Try Cato
The Solution that IT teams have been waiting for.
Prepare to be amazed!
Innovate, grow and thrive
With a true SASE platform
With Cato, any organization can reap the full benefits of digital transformation, move at the speed of business, and be ready for whatever’s next.




