Cato’s DNS Security inspects all DNS traffic, preventing malicious DNS activity hiding within the protocol’s traffic, and blocking DNS requests to malicious destinations before a connection is made.
Phishing is one of the top attack vectors that every CISO is concerned about.
Ongoing training of AI and ML algorithms on Cato’s massive global data lake enables Cato DNS Security to provide in-line identification of domain squatting and other website impersonation attempts. This is achieved through real-time analysis of webpage components, domain age, popularity, and patterns associated with toolkits used in phishing sites. This Inline detection of phishing attacks helps prevent credential harvesting, malware delivery, and sensitive data loss.
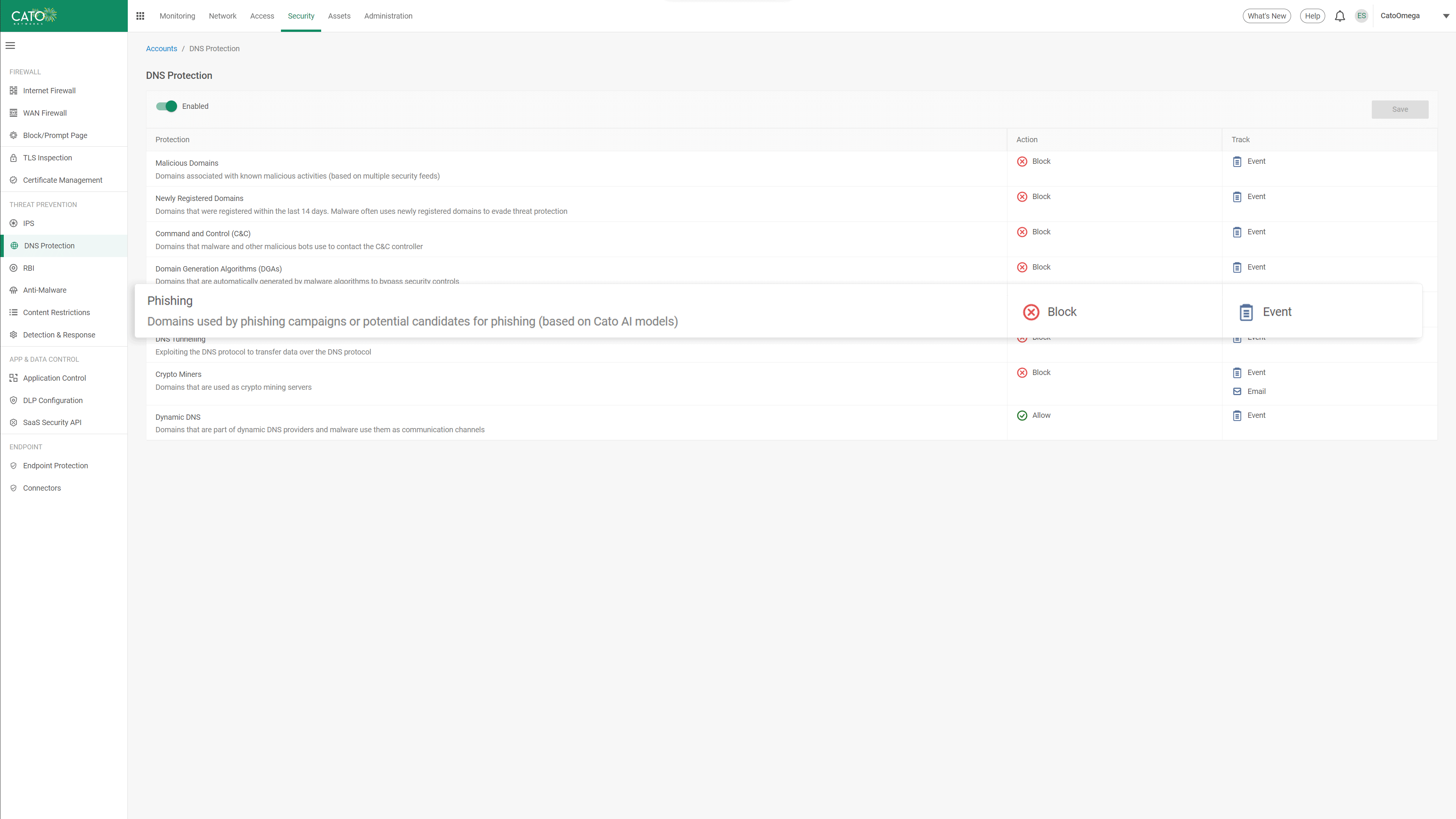
The number of malicious sites that host command and control (C&C) servers to remotely manage malware is huge. Attackers continuously move their C&C servers between sites to avoid detection and blacklisting. Cato DNS Security uses Cato’s timely and continuously optimized threat intelligence system to identify malicious domains and C&C sites and block traffic to and from them in real time. Using Cato DNS Security, enterprises dramatically reduce exposure to millions of web-based attacks with near-zero false positives.
DNS tunneling attacks leverages the need to allow DNS traffic to pass through security controls, as a method for data exfiltration and C&C access. Cato’s DNS Security analyzes DNS request properties such as packet size, record type, and the ratio of unique subdomains to identify anomalies and indicators of DNS tunneling attacks. Cato’s AI/ML algorithms are continuously trained to identify DNS Tunneling, enabling protection that is not dependent on specific knowledge of the threat actor or domain name.
Crypto miners use compromised corporate endpoints for financial gain leading to system instability, poor user experience, and increased costs for the organization. Cato leverages dedicated rules and heuristics to identify domains that are used for crypto-mining operations, blocking any DNS requests to these destinations. With Cato, enterprises protect users’ productivity and security from impact by unauthorized use.
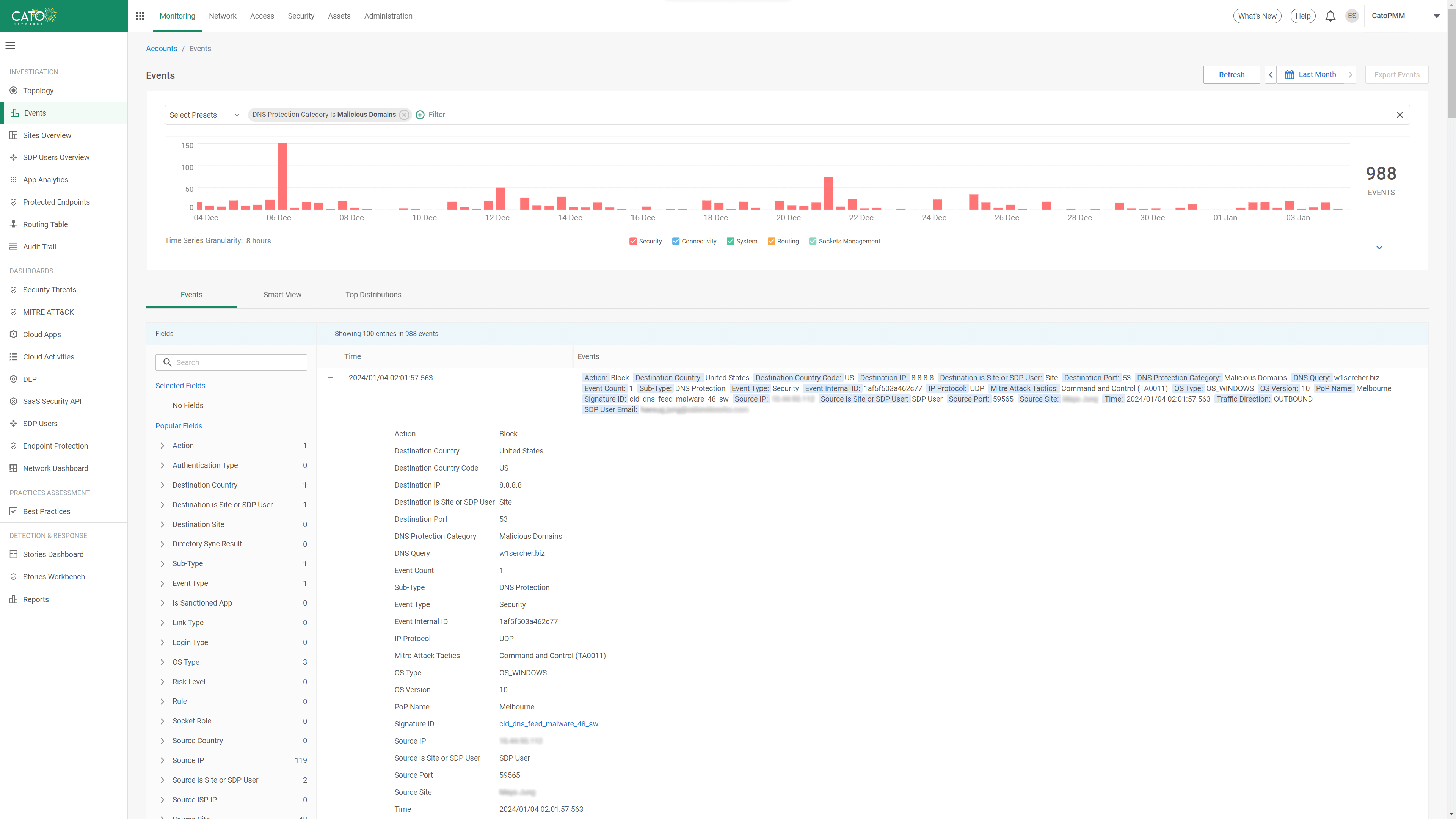
All threat activity is logged in Cato’s global data lake, providing administrators with instant access to the threat information they need via a single console. DNS security events are visible in the security threats dashboard with filtering and drill down capability into all events related to DNS protection. Security teams can quickly understand and evaluate DNS threats to their organization without aggregating multiple data sources or navigating between multiple consoles.
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“Cato future-proofs Swissport’s IT infrastructure. The platform constantly evolves, adapts to new technologies, and provides the visibility and security we need to support our business today and tomorrow.”
The Solution that IT teams have been waiting for.
Prepare to be amazed!