Universal Zero Trust Network Access (ZTNA)
Universal Zero Trust Network Access (ZTNA) allows organizations to create a single access policy to enterprise resources based on risk and least privilege principles, and enforce it on all users regardless of location – in the office, at home or remote.
Single, Risk-based ZTNA Policy Everywhere
Cato’s Universal ZTNA uses a single risk-based policy to control user access to sensitive data using identity and a variety of access context attributes including device security posture, user geography, application risk, and compliance ratings. Cato consistently enforces ZTNA policies across its global cloud service and all users regardless of their location – office, home, or remote.
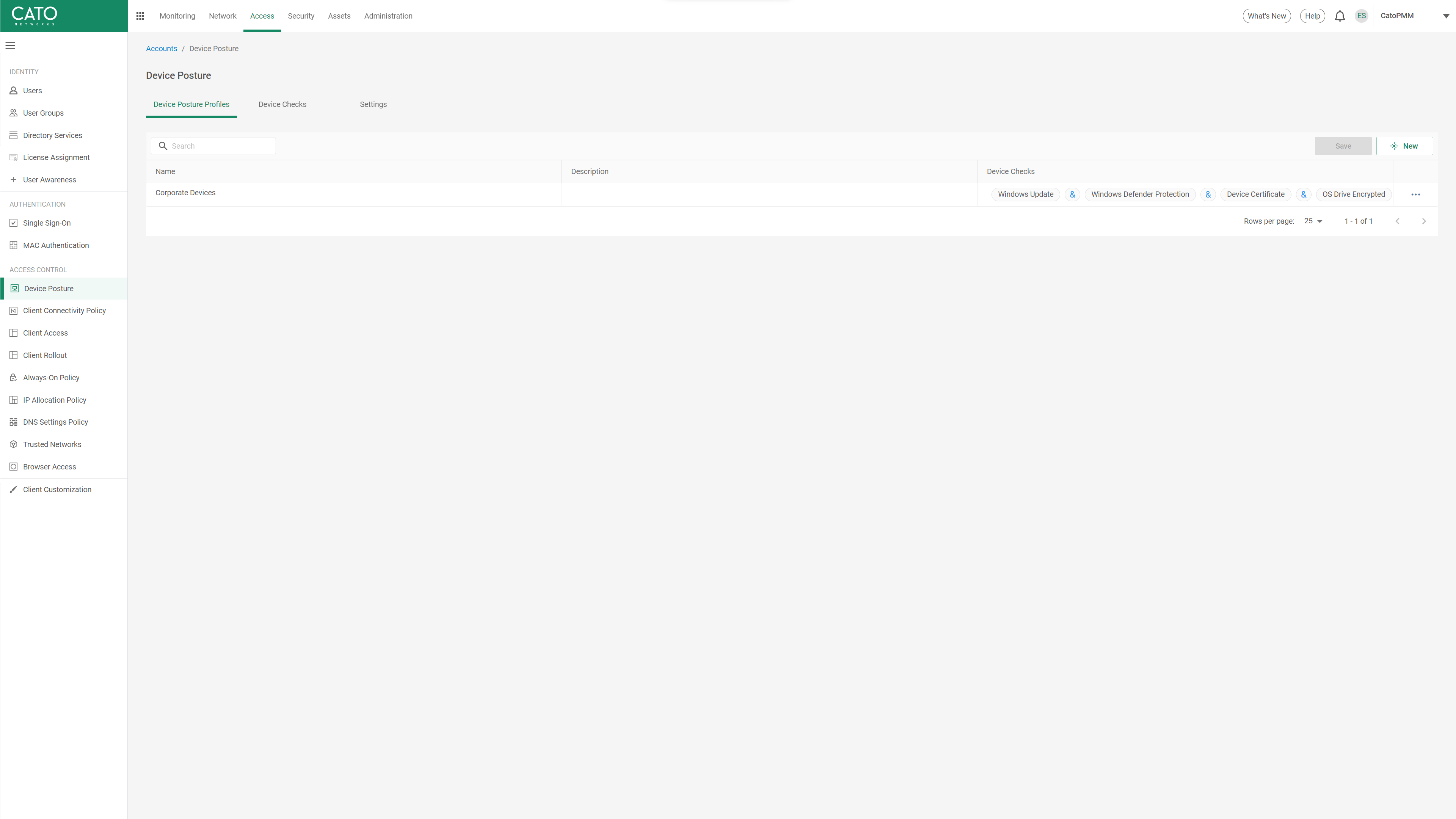
Continuous Device Posture Evaluation
Cato evaluates connected device posture, including operating system and patches, anti-virus, disk encryption, device firewall, geographic location, and device certificate at connection and throughout the session. If a posture check fails, Cato can terminate the user’s connection entirely or block access to specific resources until the device becomes compliant. Continuous device posture evaluation strengthens the security posture of organizations by ensuring devices meet a minimum set of requirements, reducing the risk of data breaches from compromised endpoints.
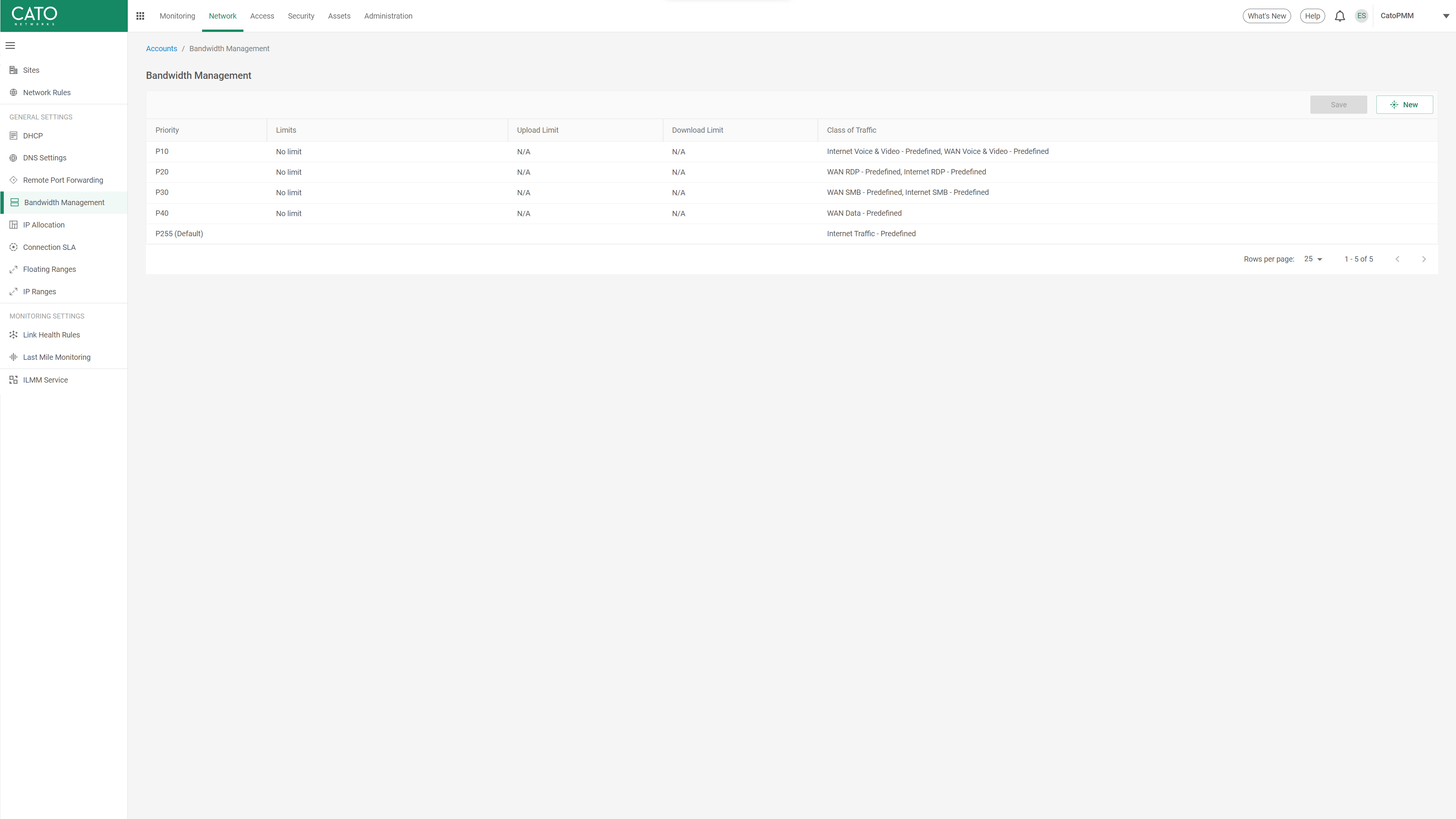
Application Optimization for Consistent User Experience
Remote users often complain about application performance degradation, impacting their productivity. This is typically a result of an unreliable internet connection and traffic backhauling to a central location for security inspection.
The Cato SASE Cloud Platform includes a global private backbone that features robust optimization and QoS capabilities, targeted to deliver optimized access to cloud and on-premises resources from anywhere. With Cato, remote users connected to The Cato SASE Cloud Platform enjoy the same optimized application access as users at office locations, ensuring optimal user experience and maximum productivity, without security compromises.
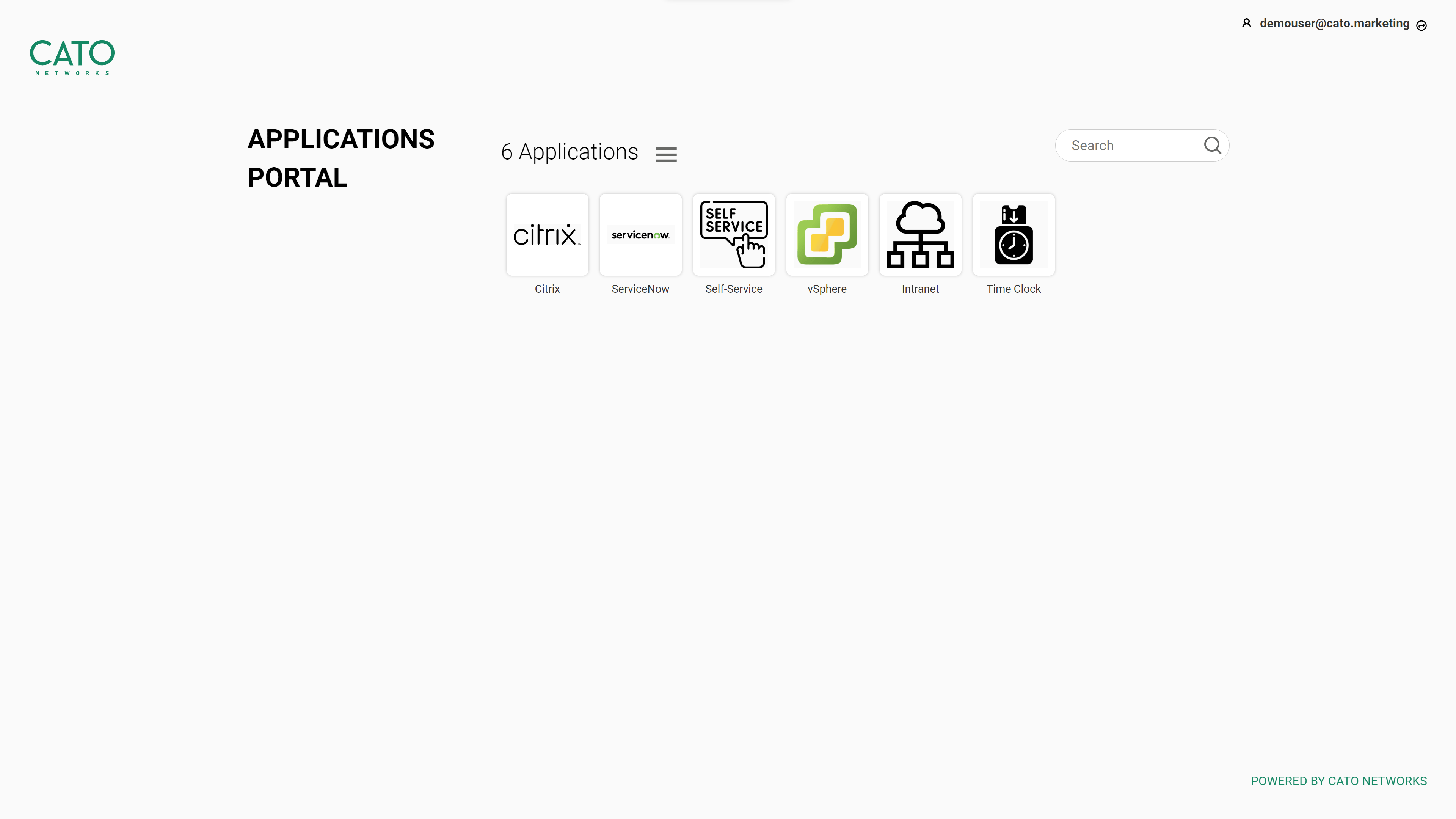
Clientless Application Access for 3rd-parties and BYOD
Cato natively supports browser-based clientless access to private applications for users who can’t use the Cato Client. Admins can easily publish applications to a web portal, create access policies, and enable instant secure application access for any user. Cato’s clientless access requires minimal setup and can be deployed with secure authentication from an external SSO and MFA provider of your choice or using Cato’s user database.
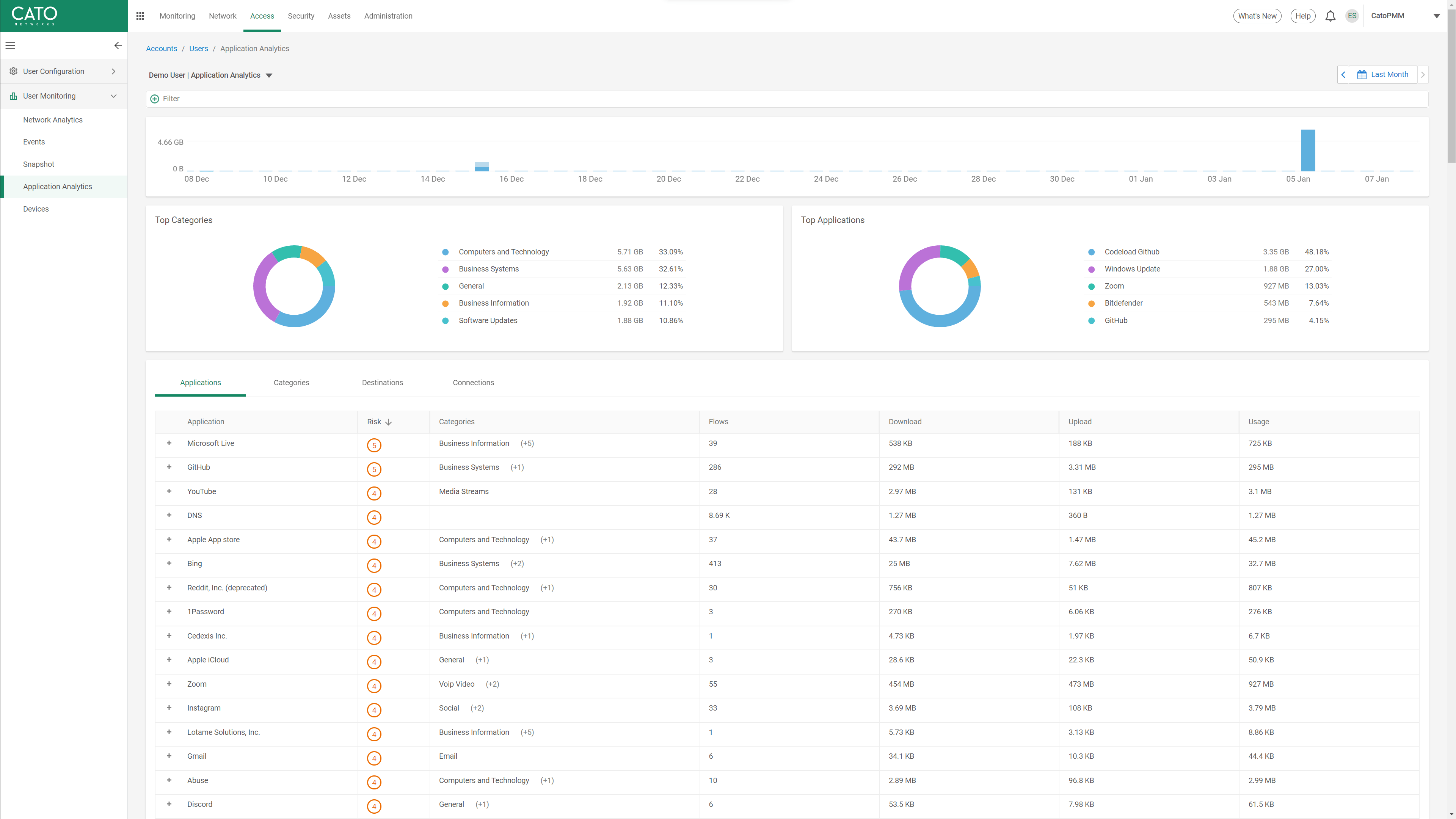
Full Remote Access Visibility and Control
Cato provides administrators and auditors a dedicated dashboard to monitor remote user connectivity and activity. The dashboard shows currently connected users, their location, their source device and posture, and their application usage analytics. One-click filtering allows further per-user analysis, for related networking, access, and security events which can support the creation of new access policies.
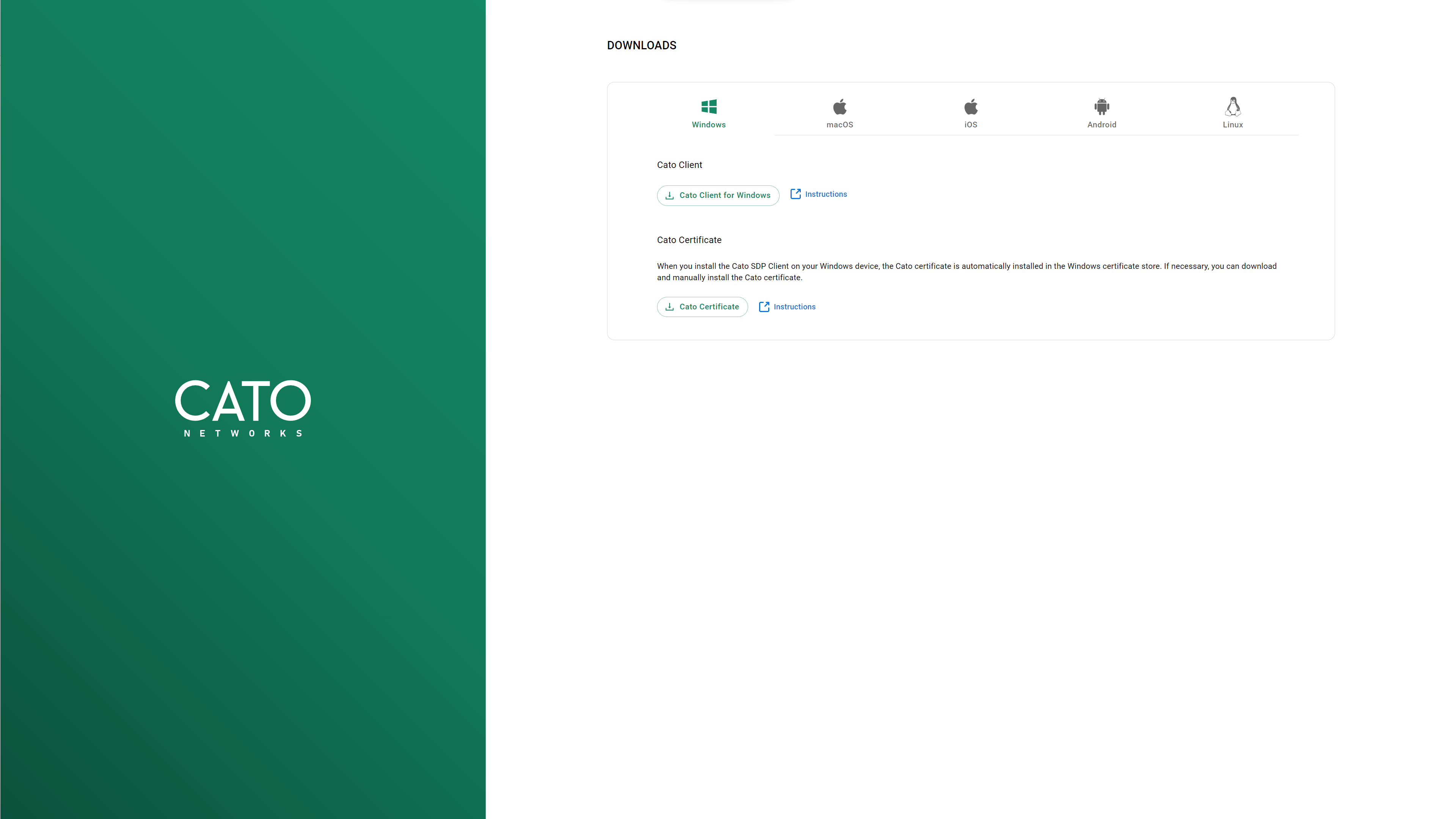
Corporate, BYOD, and Wide OS Support for Every Use Case
Cato Universal ZTNA client supports Windows, MacOS, iOS, Android, and Linux for maximum coverage, regardless if the device is corporate-owned or BYOD. To help admins seamlessly migrate from their legacy VPN to the Cato Universal ZTNA, central deployment via common Mobile Device Management (MDM) is supported. A self-service portal for user provisioning is available for external contractors and enterprises who do not use MDMs.
Continuous Threat Prevention and Data Protection
Cato continuously evaluates all user traffic for threat prevention and data protection. Cato’s Single Pass Cloud Engine (SPACE) inspects the user’s session traffic using multiple security engines including FWaaS, SWG, IPS, NGAM, CASB, DLP, RBI, and more. Malicious traffic and unauthorized access to sensitive data are identified, audited, and blocked. Cato helps enterprises address remote access, threat prevention, and data protection requirements using a single platform, avoiding complex routing and integration projects often needed to support remote access cases.
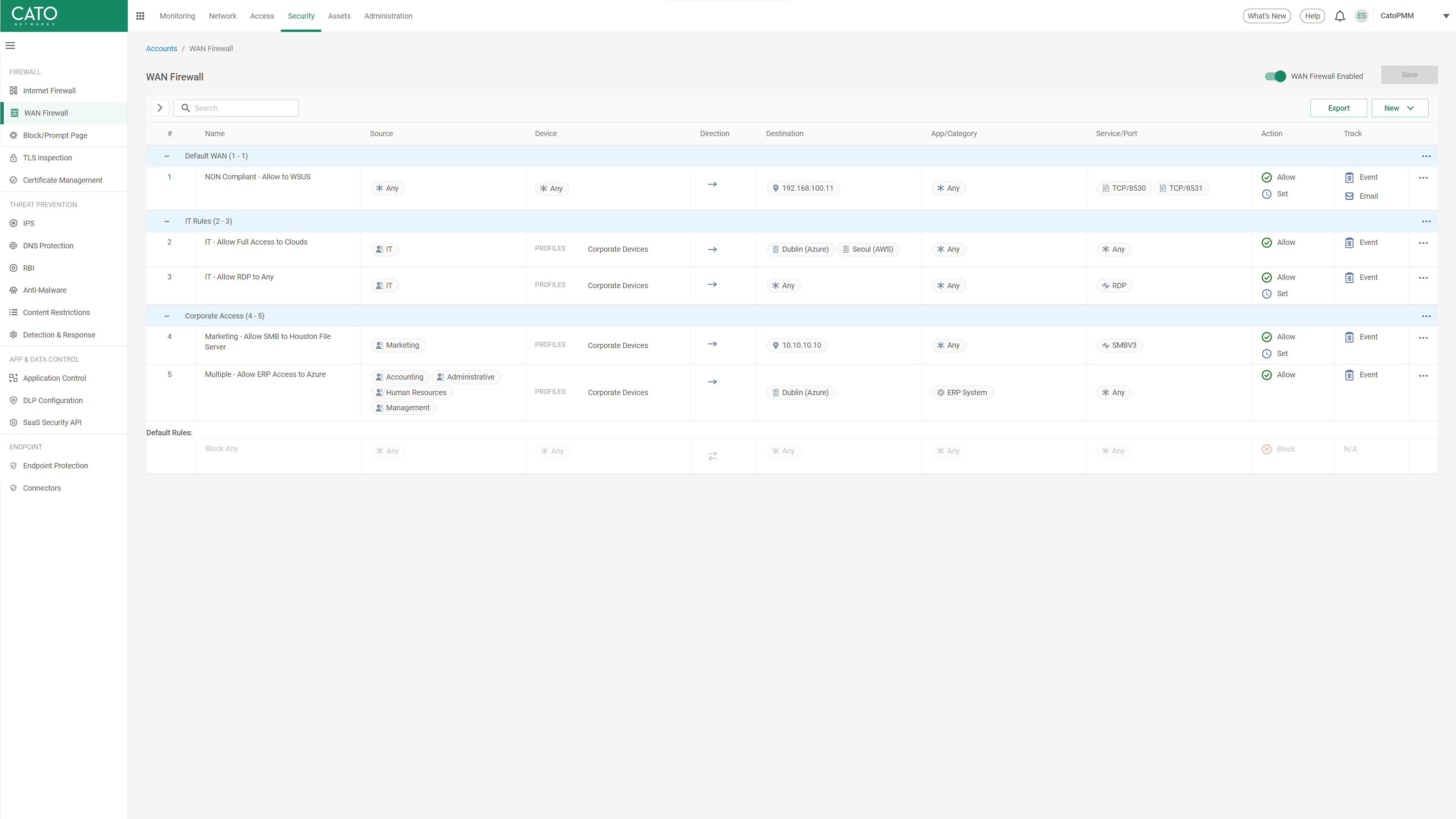
Zero Trust Network Access Video Demo
Cato’s SASE platform offers full-mesh connectivity for all users and locations connected to the service. Granular, context-aware policies are defined in the WAN firewall rules. By default, users can only access explicitly permitted resources, with clientless access options and comprehensive visibility and event tracking.
Cato SASE Cloud Platform Powers the Digital Business
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks Named a Leader in the Gartner® Magic Quadrant™ for Single-Vendor SASE 2024
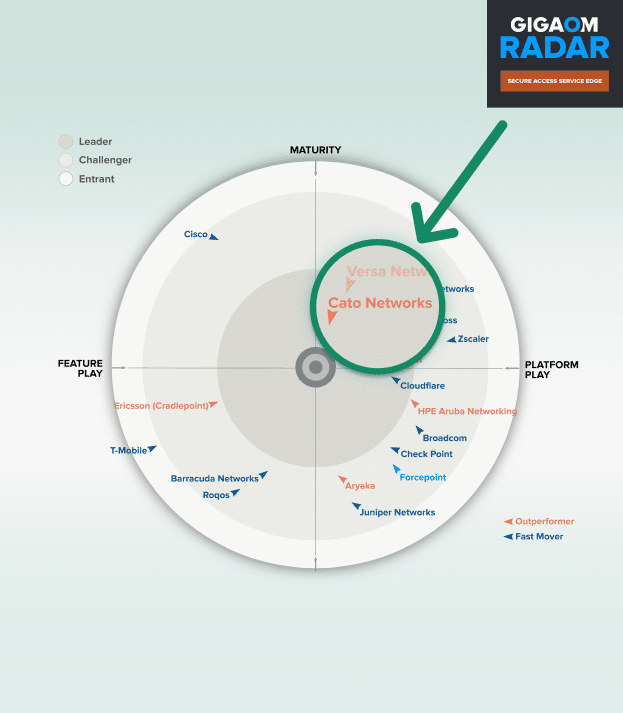
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
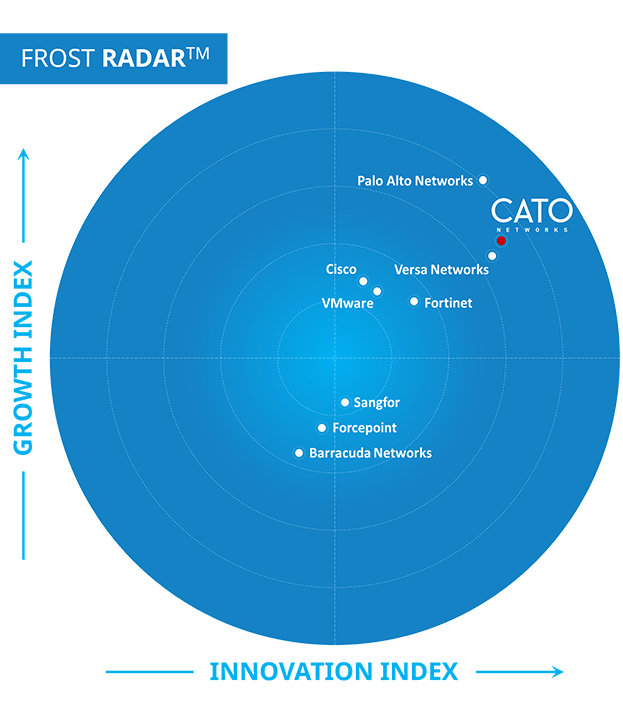
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
Try Cato
The Solution that IT teams have been waiting for.
Prepare to be amazed!